🔎 Unit Overview
In this unit you will gain an awareness of:
- The importance and value of data
- How human actions can make data more vulnerable to theft or exploitation
- Common cyberattacks
- Measures put in place on networks to help protect IT systems from attacks
🎯 Learning Objectives
- Explain the difference between data and information
- Critique online services in relation to data privacy
- Identify what happens to data entered online
- Explain the need for the Data Protection Act
💬 Key Vocabulary
- data
- information
- cybersecurity
- cybercriminals
- profiling
- user behaviour
- privacy policies
- data protection
- data subject
- data portability
- malware
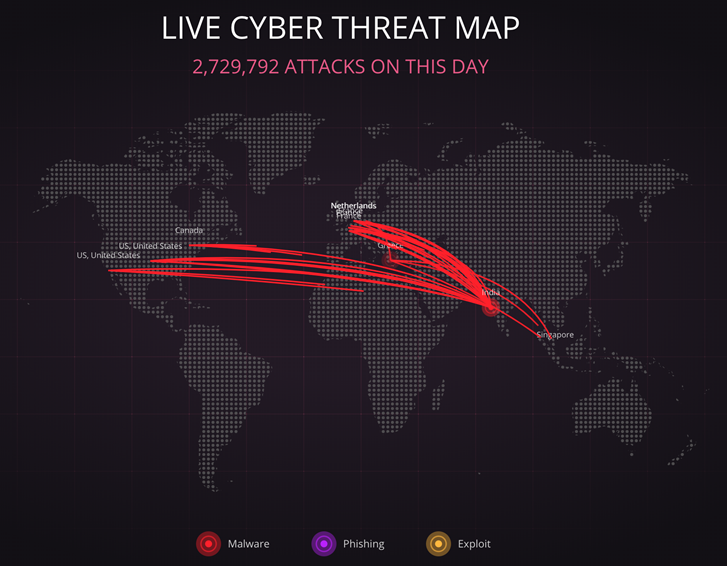
📝 Starter Activity – Motives behind attacks
Click this link: https://threatmap.checkpoint.com/
Look at the cyberattacks that are happening right now.
What might some of these attacks be trying to steal or get access to?
📖 Data vs Information
Data is raw facts and figures with no context:
John: 28
Claire: 49
Jade: 40
Ahmed: 45
Chloe: 38
Information is created when that data has been processed and becomes meaningful:
These are scores from a test where the pass mark was 35.
John needs to resit the test.
The average score is 40.
📝 Level 1 – Customer Data
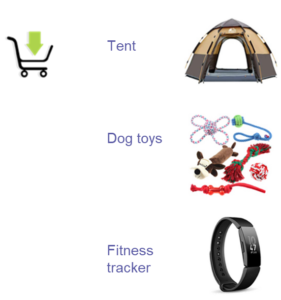
This data is the contents of a shopping basket for an online customer.
This data can be used to help build a profile of this customer and therefore convert the data into information.
What assumptions can you reasonably make about this customer?
Download the Level 1 activity and answer the questions.
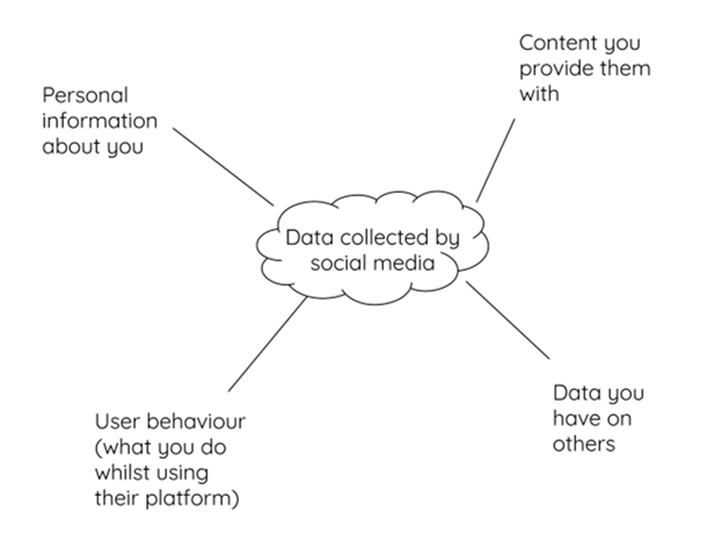
📝 Level 2 – Categorise the data
Complete the mind map by adding example data next to each category.
Download the Level 2 activity to do this.
Example
Personal information about you:
- Name
- Date of birth etc.
📖 Privacy policies: Be informed
Work in pairs and decide which two of the companies on the right-hand side you wish to research. In your pairs, allocate one each.
Spend five minutes researching the question, ‘What data do these companies collect about their users?’
Add your new findings to your mind map and spend two minutes discussing them with your partner.
📖 The consequences of data theft
Watch this video
If cybercriminals successfully steal data from companies, who would suffer and in what way?
📖 Data Protection Act 2018
In 2018 the UK implemented the European Union’s General Data Protection Regulations (GDPR) into UK law with the Data Protection Act. It states that all organisations and people using and storing personal data must abide by the following principles.
Data must be:

📖 Data Protection Act 2018 – Your rights
Anyone whose data is stored when using a computer is counted as a data subject. As a data subject, you have the right to find out what information the government and other organisations store about you.
You have the right to:

📝 Level 3 – Quick Quiz
Download the Level 3 activity and complete the four questions to summarise your learning today.
🏅 Level Up
🥇 Level 1
- Complete the Level 1 worksheet and upload the completed file to Teams.
🥈 Level 2
- Complete the Level 2 worksheet and upload the completed file to Teams.
🥉 Level 3
- Complete the Level 3 worksheet and upload the completed file to Teams.
In this lesson, you…
- Looked at the difference between data and information
- Investigated what data companies might collect on you, as well as how that data might be valuable to cybercriminals
- Looked at the need for the law involving data protection
Next lesson, you will…
- Look at the risk of data being compromised through human error, and strategies that can be put in place to avoid the dangers