🎯 Learning Objectives
- Define hacking in the context of cybersecurity
- Explain how a DDoS attack can impact users of online services
- Identify strategies to reduce the chance of a brute force attack being successful
- Explain the need for the Computer Misuse Act 1990
💬 Key Vocabulary
- cyberthreats
- hacking
- ethical hacking
- penetration testing
- brute force attacks
- DoS (denial of service)
- DDoS (distributed denial of service)
- Computer Misuse Act (1990)
- script kiddies
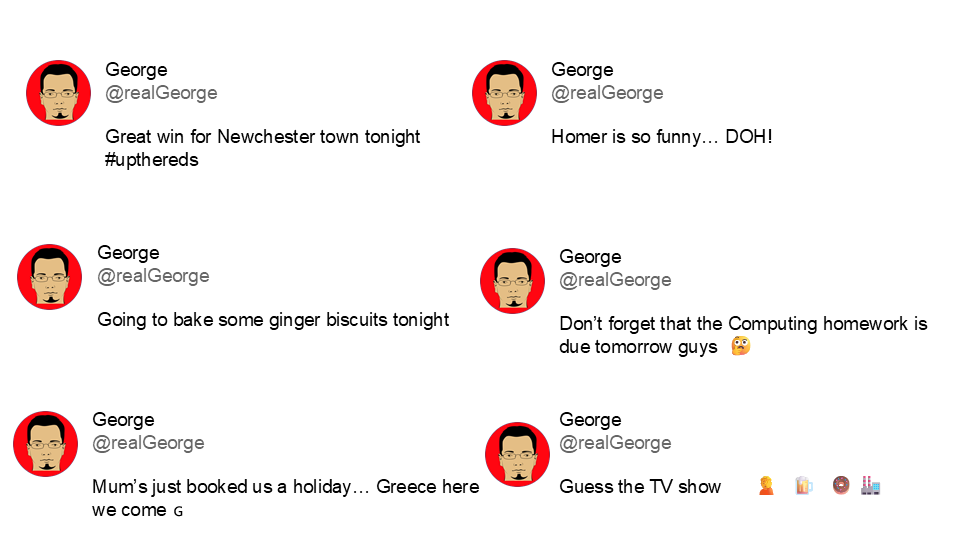
📝 Starter Activity – Hack George’s account
George’s phone has run out of battery and his family are worried about where he is.
They’ve asked you to hack his FakeBook account to see if you can find out where he is tonight.
Use the login page link on the right-hand side.
Check his social media account below to see if you can find any clues to help you out.
📖 Hacking
Hacking in the context of cyber security is:
Gaining unauthorised access to or control of a computer system
Why might people want to hack?
Answer
- To steal data
- To disrupt services
- For financial gain
- For political reasons (espionage and activism)
- For fun (planting the flag)
- For ethical reasons
📖 Unethical versus ethical hacking
A company is harming animals by testing their cosmetic products on them.
Is it ethical to hack into their systems to find the data that will expose their practice to the whole world?
A company wants to employ hackers to see if they can find any weaknesses in their system.
Is it ethical for a hacker to do this, to help the company so that they can improve their security?
What are these hackers called?
These kinds of hackers are called penetration testers (pen testers) are people who are paid to legally hack into computer systems with the sole purpose of helping a company identify weaknesses in their system.
📖 Case study: Hacktivism
Hacktivists are rarely motivated by theft, but are more interested in creating disruption to cause public embarrassment or to promote a cause. Motives might be:
- Political
- Protesting, for example for civil liberties or against climate change
- Targeting major corporations that they feel are doing something wrong
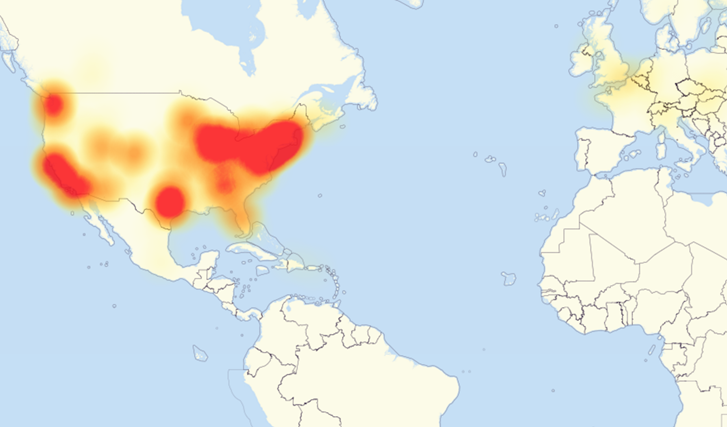
“It was initially thought that the 2016 Dyn cyberattack was the work of New World Hackers, but it later emerged that it was probably done by script kiddies.”
https://en.wikipedia.org/wiki/hacktivism
📖 Script kiddies
Script kiddies are hackers (not necessarily kids) who use tools downloaded from the internet that allow them to hack with little technical knowledge.
Is it thought that the 2016 Dyn cyberattack was done by script kiddies using a DDoS attack.
📖 Denial of service attack (DoS)
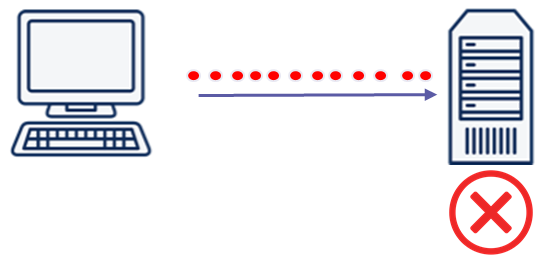
This is a cyberattack in which the criminal makes a network resource unavailable to its intended users.
This is done by flooding the targeted machine or website with lots of requests from a single computer in an attempt to overload the system.
📖 Distributed denial of service attack (DDoS)
This uses the same concept as a DoS attack, but this time it is multiple computers making the attacks at the same time.
It is a lot harder to:
- Stop the attack by simply blocking a single source.
- Identify who is responsible, as lots of machines are making requests, many of them because they are infected by malware.
📝 Level 1/2 – Brute Force Attack
This is a form of attack that makes multiple attempts to discover something (such as a password).
Download and open the Level 1/2 activity below.
📖 The Computer Misuse Act (1990)
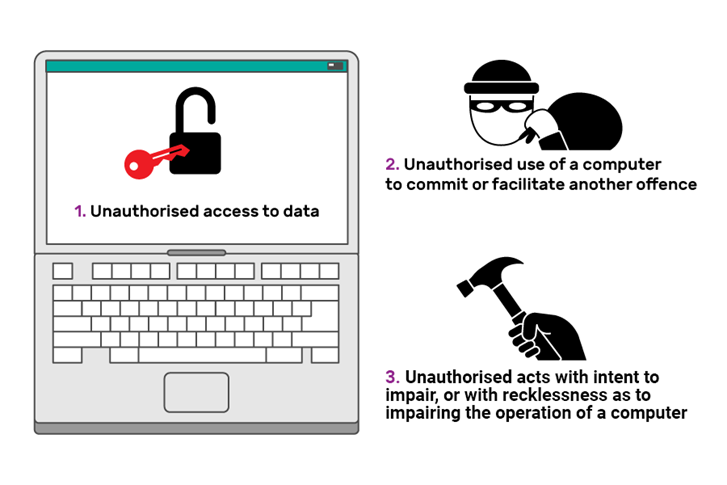
This was passed by Parliament and established three new offences:
- Section 1: Unauthorised access to computer material
- Section 2: Unauthorised access with intent to commit or facilitate the commission of further offences
- Section 3: Unauthorised acts with intent to impair, or with recklessness as to impairing, the operation of a computer
The Computer Misuse Act (1990) Fact Sheet
The Computer Misuse Act (1990) and its amendments were created so that unauthorised access to computers and crimes committed using a computer could be prosecuted. The act is based on three principles and makes the following actions illegal:
| Law | Punishment |
|---|---|
| Section 1: Unauthorised access to digital/computer material. This means a person asking a computer to perform any function with the intent of accessing anything on the computer for which they do not have permission, and for which they know they do not have permission. | Punishable by up to two years in prison and a £5,000 fine. |
| Section 2: Unauthorised access to digital/computer material with intent to commit or facilitate the commission of further offences. This means a person gaining access to a computer without permission in order to commit another crime or to enable someone else to commit a crime. | Punishable by up to five years in prison and an unlimited fine determined by the damage caused and the severity of the crime. |
| Section 3: Unauthorised acts with intent to impair, or with recklessness as to impairing, the operation of a computer. This means a person intentionally impairing the operation of any computer or program, or intentionally preventing access to any data or program on any computer. This includes creating or supplying materials that could be used to carry out this offence. | Punishable by a prison sentence of up to ten years and an unlimited fine, but if the act puts life at risk or endangers national security, the sentence can be extended to life imprisonment. |
📝 Level 3 – The Dyn cyberattack
The Dyn cyberattack we discussed earlier was a DDoS attack.
Answer the following three questions in a blank Word file:
- Which of the three sections of the Computer Misuse Act (1990) does a DDoS attack violate?
- Why do you think this?
- What is the maximum punishment for this crime under this act?
When all three questions are completed, upload the Word file to Teams.
🏅 Level Up
🥇 Level 1
- Complete Level 1 from the Level 1/2 worksheet and upload the worksheet to Teams.
🥈 Level 2
- Complete Level 2 from the Level 1/2 worksheet and upload the worksheet to Teams.
🥉 Level 3
- Answer the three questions in a new Word file and upload the completed file to Teams.
In this lesson, you…
- Investigated common strategies used by hackers
- Identified strategies to reduce the chance of a brute force attack being successful
- Explained the need for the Computer Misuse Act
Next lesson, you will…
- List the common malware security threats for devices
- Explain how devices can be protected from common security threats